Blockchain 101: Blockchains and Consensus Mechanisms
Jan 18, 2022
Never miss our publications about Open Source, big data and distributed systems, low frequency of one email every two months.
Cryptocurrencies are booming in 2021, with a market cap moving from 750 to more than 3,000 billion dollars. Let’s face it, this is mainly due to speculation. A lot of people involved do not have a clue of what is behind the tokens they invest in.
But if we put that aside and look at the technical fundamentals, we can acknowledge that 2020-2021 are bringing along a bunch of new blockchains with better, faster (viable?) consensus mechanisms, like Proof of Stake, and new widely used applications, like decentralized finance (DeFi) and Non-fungible tokens (NFTs).
Before going into those, we need to take a step back: What is a blockchain? A cryptocurrency? A Proof of Work? A block? A wallet? A smart contract? The Ethereum Virtual Machine (EVM)? An ERC-20 token? An NFT? Decentralized Finance (DeFi)? Oracles?
This article is the first of a series of 3 that focuses on the technical fundamentals behind crypto:
- Blockchain 101: Blockchains and Consensus Mechanisms
- Blockchain 102: Cryptocurrencies, Wallets and DApps
- Blockchain 103: The EVM Ecosystem, a Good Entry Point for Devs
Disclaimer: Not a financial advice.
What is a blockchain?
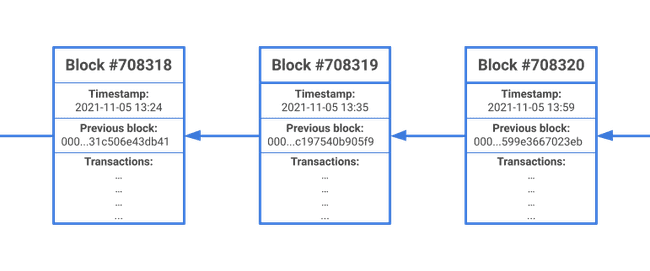
A blockchain is a decentralized trustless peer-to-peer database that stores a special type of data: blocks. Blocks are immutable and ordered into a chain, one block having only one preceding and one following block. Thus the term “blockchain”.
One block consists of:
- A timestamp;
- A bunch of records;
- A pointer to the previous block (its hash).
In most popular blockchains (e.g. Bitcoin, Ethereum), also called distributed ledgers, the records stored by blocks are transactions. Example of transactions: coin transfers or function calls (more on this later).
Consensus mechanisms
Most blockchains are permissionless: everyone is free to add servers to the network and to interact with the blockchain, including malicious actors. Blockchains had to come up with consensus mechanisms that ensure that every block written to the database is valid.
Those consensus mechanisms rely on cryptography and game theory: it has to be more profitable to write legitimate transactions in blocks than to try to write false transactions (e.g. create coins out of nowhere).
Proof of Work
Proof of Work (PoW) was the first consensus mechanism to be designed and implemented. Bitcoin and Ethereum, the most popular blockchains around, are based on PoW and have proven to be unbreakable: they have never been hacked.
Let’s dive into the Bitcoin implementation of PoW. It will help us understand how cryptography and game theory are used together in blockchain. I assume that you know what a hash is in the following section.
Mining
You have probably already heard the term “mining”, which means participating in adding blocks to the blockchain.
To be added to the blockchain, a block is associated with its hash (that will be referenced by the next block). The block’s hash is computed on:
- The block’s timestamp;
- The block’s transactions (the number of transactions contained in the block is limited by the maximum block size: 1 MB for Bitcoin);
- The previous block’s hash;
- A nonce (a number that is chosen to match specific conditions).
The hash has to satisfy the following condition to be accepted by the network: be smaller than the target hash. A target hash is a numerical value in hexadecimal used to set the difficulty of the mining process. It can be adjusted to raise it or lower it, hence adapting the mining rate. (E.g. for Bitcoin, the target hash is adjusted by the network so that one block is mined every 10 minutes).
A typical target hash looks like this: 0000000000000000000633b91a8cd72235104935c9d3af0b0edae9ad6f89f4ef. The number of leading zeros is what makes the hash difficult to find because it decreases the size of the target hash.
The only modifiable piece of a block is the nonce. So to find the right hash, miners (blockchain nodes) have to iterate on all the possible nonces until they find the right one.
# Algorithmic approximation of mining a block
block_nonce = 0
while block_hash > TARGET_HASH:
block_hash = hash(
1635971597, # Block timestamp
'00000000...0edae9ad6f89f4ef', # Previous block hash
'f5ef4359...efe2bf58b7c02557', # Transactions hash
block_nonce # Nonce
)
block_nonce += 1
add_to_chain(...)Take a look at what a Bitcoin block looks like on an explorer: for example on Blockchain.com Bitcoin Explorer!
Block rewards
The first miner to find a matching nonce is rewarded with some Bitcoins, but only if the block is further validated by other peers.
This rule makes all the miners compete with each other and lead to miner servers being more and more powerful to win Bitcoins. Miner servers are therefore expensive to buy and power.
Game theory enters into play at this point: to have a chance of winning the race to mine a block, one has to spend a lot of money on material and energy; and to win money (= Bitcoins) the transactions that are in the block have to further be validated by the network (peers). If a miner tries to push false transactions, the block will not be validated and the miner not rewarded. Therefore, he will lose the money put into the mining process!
Immutability enforced by cryptography and game theory
Relying on hashes ensures that the blockchain is immutable: altering a single transaction in a block would totally change the block’s hash. But because the next block the latter’s hash, its hash would also change!
Application developers using Git are familiar with this concept: any change to a previous commit generates a divergent hash for all the later commits and the branch will then diverge from remote.
Let’s say that someone wants to alter a transaction that occurred 4 blocks ago, he will have to:
- Find the nounce for the altered block (using only the power of a few accomplice miners);
- Find the nounce for each of the 4 next blocks, because their hashes would all be changed;
- Make the network validate the blocks.
We can imagine that this process will cost a huge amount of energy with poor chances of success: it is not worth trying!
Proof of Work limitations
The PoW consensus mechanism is great at securing the Bitcoin blockchain but it is:
- Slow: 1 block every 10 minutes;
- Costly and bad for the environment: a lot of material and power are needed;
- Does not scale well: a lot of the work is done for nothing because the miners are competing;
- Sensible to the 51% attack: if an organization owns more than 51% of the miners, it can choose which transactions are allowed to be written to the blockchain by invalidating blocks.
All these limitations led to the design of new consensus mechanisms.
Proof of Stake
Proof of Stake (PoS) is the most widely adopted alternative to PoW. In PoS, nodes are not called miners but validators and have to stake (= lock) a big number of tokens to participate in block validations.
For every block, a group of validators is picked for validation (that is often quorum-based). The number of blocks that a validator is involved with is proportional to the size of its stake: if it has 1% of the blockchain coins, it will be picked for 1% of the validations.
Like in PoW, nodes are rewarded when validating blocks and cryptography is used to ensure immutability.
There are a lot of different implementations of PoS, here are some examples:
- Tower BFT, used by the Solana blockchain;
- Avalanche Consensus, used by the Avalanche blockchain;
- Tendermint, used by blockchains built with the Cosmos SDK.
Other mechanisms?
Other consensus mechanisms than PoW and PoS exist, but none of them has yet reached massive adoption.
Conclusion
In this article, we have scratched the surface of the functioning of blockchains and consensus mechanisms. In the next one, we will talk more about how to interact with distributed ledgers and blockchain.
If you want to find out more, there is a lot of great detailed documentation around. Some examples: